 |
市場調查報告書
商品編碼
1938978
網路安全:市場佔有率分析、產業趨勢與統計、成長預測(2026-2031)Cybersecurity - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2026 - 2031) |
||||||
※ 本網頁內容可能與最新版本有所差異。詳細情況請與我們聯繫。
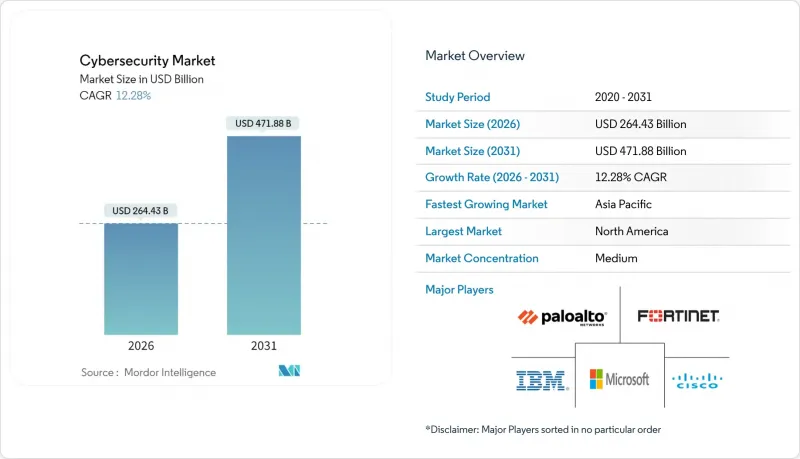
預計到 2026 年,網路安全市場規模將達到 2,644.3 億美元,高於 2025 年的 2,355 億美元。
預計到 2031 年將達到 4,718.8 億美元,2026 年至 2031 年的複合年成長率為 12.28%。
這一成長主要受零信任架構投入增加、IT與操作技術(OT)防禦整合以及量子加密準備工作的推動。北美仍保持其支出主導地位,而亞太地區則經歷了最快的成長,因為企業正將工作負載遷移到雲端優先環境。此外,由於網路保險承保人要求檢驗的控制措施,預算撥款也在增加,促使企業轉向能夠簡化監控的整合安全平台。同時,隨著供應商競相應對新的攻擊手法,透過併購的平台整合也不斷增加。
全球網路安全市場趨勢與洞察
加速雲端優先的數位轉型
隨著分散式環境中邊界控制失效,雲端遷移正在重新調整安全投資的優先順序。雲端採用率持續成長,超過了本地部署的配置,並推動了對整合身分、工作負載和資料保護功能的雲端原生應用程式保護平台的需求。企業正在尋求統一的主機來減少工具的冗餘,而供應商則透過提供能夠關聯混合環境中遙測資料的平台來回應這一需求,從而提高可見性和回應效率。
關鍵基礎設施中IT與OT安全的整合
工業4.0的推進正將傳統上與空氣間隙的系統接入網路,使傳統控制網路暴露於與攻擊IT資產相同的攻擊者之下。這推動了網路安全市場的需求。諸如ISA/IEC 62443等法規結構要求建構從工廠車間到資料中心的整合防禦體系,從而促進了對專用OT威脅偵測和隔離工具的投資。隨著國家級駭客對電網漏洞的偵測,能源供應商正主導這一趨勢,而OT專用安全措施帶來的風險降低效益也超過了同類IT計劃。
網路安全人才短缺和薪資上漲
網路安全專業人員短缺340萬人,加之雲端運算、營運技術(OT)和人工智慧驅動的防禦等稀缺技能人才薪資不斷上漲,令預算捉襟見肘。這種限制因素正推動市場整合,轉向專業人員需求較少的平台,同時也為提供資安管理服務和人工智慧自動化工具的供應商創造了機會。此外,網路安全專業人員的高離職率也加劇了這一局面,64%的網路安全專業人員因工作壓力過大而考慮換工作。這導致招募和培訓成本不斷攀升,持續影響企業的安全預算。
區域分析
北美地區擁有成熟的法規環境和許多主要供應商,預計到2025年將佔全球網路安全市場收入的43.20%。受第14028號行政命令下廣泛推行的零信任政策的推動,該地區到2027年的網路安全支出預計將超過1,376億美元。 2023年,美國共發生9,036起網路安全事件,遠超歐洲的2557起,這持續推動了對高階威脅情報和託管安全營運中心(SOC)服務的需求。加拿大和墨西哥正透過公私合作項目,協調跨境外洩報告和事件回應,為市場成長做出貢獻。
亞太地區以16.85%的複合年成長率 (CAGR) 實現最快成長,各國主導的數位化國家計劃將網路安全提升至關鍵基礎設施層級。中國、印度、日本和韓國已為國家網路安全戰略撥出多年預算,而澳洲和紐西蘭則實施了全面的彈性框架,強制要求揭露安全事件。該地區的買家通常從一開始就採用雲端原生安全,從而跳過傳統的控制措施,加速採用以身分為中心和人工智慧驅動的分析技術。
歐洲的成長主要得益於GDPR和NIS2指令的實施,後者將適用範圍擴大到更多產業。德國、英國和法國是主要的支出國,而中東歐市場則在適應歐盟要求的過程中,從小規模的基數上成長。法國和西班牙的主權雲端計畫刺激了對本土託管安全架構的需求,而跨境資料傳輸限制則加速了隱私增強加密技術的普及。
其他福利:
- Excel格式的市場預測(ME)表
- 3個月的分析師支持
目錄
第1章 引言
- 市場定義與研究假設
- 調查範圍
第2章調查方法
第3章執行摘要
第4章 市場情勢
- 市場概覽
- 市場促進因素
- 借助雲端優先加速數位轉型
- 關鍵基礎設施中IT與OT安全的整合
- 混合型勞動力的零信任架構要求
- 網路保險承保要求激增
- 數位主權監管促進區域化安全架構
- 抗量子密碼技術過渡時間表
- 市場限制
- 網路安全人才短缺和薪資上漲
- 與傳統基礎設施整合的複雜性
- API 的激增增加了攻擊面的複雜性。
- SOC警報疲勞與誤報超限投資回報率
- 價值鏈分析
- 重要法規結構評估
- 關鍵相關人員影響評估
- 技術展望
- 波特五力分析
- 供應商的議價能力
- 消費者議價能力
- 新進入者的威脅
- 替代品的威脅
- 競爭對手之間的競爭
- 主要用例和案例研究
- 定價及定價模式分析
- 網路安全培訓趨勢
- 宏觀經濟因素的影響
第5章 市場規模與成長預測
- 報價
- 解決方案
- 應用程式安全
- 雲端安全
- 資料安全
- 身分和存取管理
- 基礎設施保護
- 綜合風險管理
- 網路安全
- 端點安全
- 服務
- 專業服務
- 託管服務
- 解決方案
- 透過部署模式
- 雲
- 本地部署
- 按最終用戶行業分類
- BFSI
- 衛生保健
- 資訊科技和電信
- 工業與國防
- 零售與電子商務
- 能源與公共產業
- 製造業
- 其他
- 最終用戶公司規模
- 主要企業
- 中小企業
- 按地區
- 北美洲
- 美國
- 加拿大
- 墨西哥
- 南美洲
- 巴西
- 阿根廷
- 其他南美洲
- 歐洲
- 德國
- 英國
- 法國
- 義大利
- 西班牙
- 俄羅斯
- 其他歐洲地區
- 亞太地區
- 中國
- 日本
- 印度
- 韓國
- 澳洲和紐西蘭
- 亞太其他地區
- 中東和非洲
- 中東
- 沙烏地阿拉伯
- 阿拉伯聯合大公國
- 土耳其
- 其他中東地區
- 非洲
- 南非
- 奈及利亞
- 埃及
- 其他非洲地區
- 中東
- 北美洲
第6章 競爭情勢
- 市場集中度
- 策略趨勢
- 市佔率分析
- 公司簡介
- IBM Corporation
- Microsoft Corporation
- Cisco Systems, Inc.
- Palo Alto Networks, Inc.
- Fortinet, Inc.
- Check Point Software Technologies Ltd.
- CrowdStrike Holdings, Inc.
- Trend Micro Incorporated
- Zscaler, Inc.
- Okta, Inc.
- Gen Digital Inc.(formerly NortonLifeLock Inc.)
- Sophos Limited
- Proofpoint, Inc.
- McAfee LLC
- Darktrace plc
- Rapid7, Inc.
- SentinelOne, Inc.
- Imperva, Inc.
- Qualys, Inc.
- Trellix Holdings LLC
- Splunk Inc.
- Elastic NV
- Akamai Technologies, Inc.
- Broadcom Inc.(Symantec Enterprise Division)
- VMware, Inc.
- Cybereason
- Ivanti, Inc.
- Tenable Holdings, Inc.
- CyberArk Software Ltd.
第7章 市場機會與未來趨勢
- 評估差距和未滿足的需求
Cybersecurity Market size in 2026 is estimated at USD 264.43 billion, growing from 2025 value of USD 235.5 billion with 2031 projections showing USD 471.88 billion, growing at 12.28% CAGR over 2026-2031.
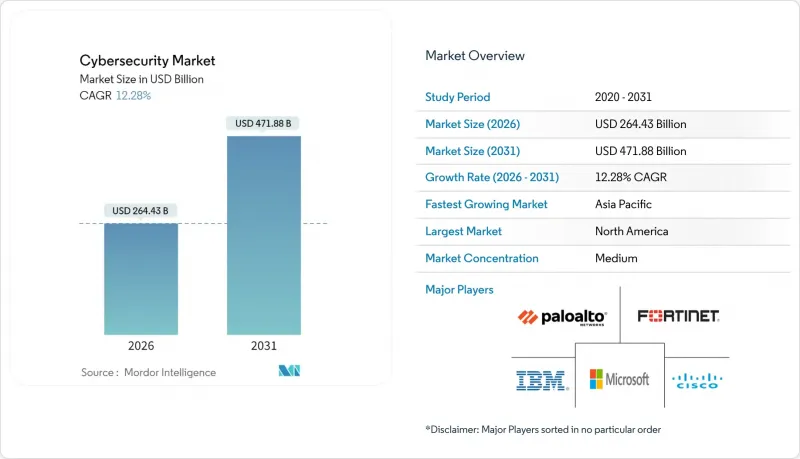
Increased spending on zero-trust architectures, the integration of IT and operational technology (OT) defenses, and preparations for quantum-ready encryption are the primary forces behind this expansion. North America retains spending leadership, while Asia-Pacific registers the most rapid gains as enterprises migrate workloads to cloud-first environments. Budget allocations are also rising as cyber-insurance underwriters demand verifiable controls, pushing organizations toward unified security platforms that simplify oversight. Simultaneously, platform consolidation through mergers and acquisitions is intensifying as vendors race to cover emerging threat vectors.
Global Cybersecurity Market Trends and Insights
Accelerated Cloud-First Digital Transformation
Cloud migration is reshaping security investment priorities as perimeter controls fail in distributed environments. Cloud deployment is growing, outpacing on-premise allocations and driving demand for cloud-native application protection platforms that integrate identity, workload, and data safeguards. Enterprises are seeking unified consoles to reduce tool sprawl, and vendors are responding with platforms that correlate telemetry across hybrid estates, improving visibility and response efficiency .
IT-OT Security Convergence Across Critical Infrastructure
Industry 4.0 forces formerly air-gapped systems online, exposing legacy control networks to the same adversaries that target IT assets, driving heightened demand in the cybersecurity market. Regulatory frameworks such as ISA/IEC 62443 now require integrated defenses that span production floors and data centers, encouraging investment in specialized OT threat detection and segmentation tools. Energy utilities are leading adoption as nation-state actors probe grid vulnerabilities, and returns on OT-focused security initiatives now exceed comparable IT projects in risk-reduction value.
Cyber-Security Talent Deficit and Wage Inflation
The shortfall of 3.4 million professionals strains budgets as salaries climb for scarce skills in cloud, OT, and AI-driven defense. This constraint is driving market consolidation toward platforms that require fewer specialized personnel to operate, while simultaneously creating opportunities for vendors offering managed security services and AI-powered automation tools. The situation is exacerbated by high turnover rates, with 64% of cybersecurity professionals considering job changes due to workload stress, creating a continuous cycle of recruitment and training costs that impact organizational security budgets .
Other drivers and restraints analyzed in the detailed report include:
- Zero-Trust Architecture Mandates for Hybrid Workforce
- Surge in Cyber-Insurance Underwriting Requirements
- Integration Complexity with Legacy Infrastructure
For complete list of drivers and restraints, kindly check the Table Of Contents.
Geography Analysis
North America controlled 43.20% of 2025 revenue in the cybersecurity market, underpinned by mature regulations and the presence of major vendors. Regional spending is forecast to surpass USD 137.6 billion by 2027 as Executive Order 14028 obliges extensive zero-trust migration. The United States reported 9,036 cyber incidents in 2023, dwarfing Europe's 2,557 events and sustaining demand for advanced threat intelligence feeds and managed SOC services. Canada and Mexico contribute to growth through joint public-private programs that harmonise cross-border breach reporting and incident response.
Asia-Pacific is the fastest-growing area at 16.85% CAGR, with state-backed digital-nation plans elevating security to critical-infrastructure status. China, India, Japan, and South Korea allocate multi-year budgets to national cyber strategies, while Australia and New Zealand implement comprehensive resilience frameworks that require mandatory incident disclosure. Regional buyers often leapfrog legacy controls by adopting cloud-native security from the outset, accelerating uptake of identity-centric and AI-driven analytics.
Europe region growth is propelled by GDPR enforcement and the forthcoming NIS2 directive that expands coverage to more sectors. Germany, the United Kingdom, and France headline spending, whereas Central and Eastern European markets grow from a smaller base as they align with EU requirements. Sovereign-cloud initiatives in France and Spain stimulate demand for domestically hosted security stacks, while cross-border data-transfer restrictions accelerate adoption of privacy-enhancing encryption techniques.
- IBM Corporation
- Microsoft Corporation
- Cisco Systems, Inc.
- Palo Alto Networks, Inc.
- Fortinet, Inc.
- Check Point Software Technologies Ltd.
- CrowdStrike Holdings, Inc.
- Trend Micro Incorporated
- Zscaler, Inc.
- Okta, Inc.
- Gen Digital Inc. (formerly NortonLifeLock Inc.)
- Sophos Limited
- Proofpoint, Inc.
- McAfee LLC
- Darktrace plc
- Rapid7, Inc.
- SentinelOne, Inc.
- Imperva, Inc.
- Qualys, Inc.
- Trellix Holdings LLC
- Splunk Inc.
- Elastic N.V.
- Akamai Technologies, Inc.
- Broadcom Inc. (Symantec Enterprise Division)
- VMware, Inc.
- Cybereason
- Ivanti, Inc.
- Tenable Holdings, Inc.
- CyberArk Software Ltd.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Market Definition and Study Assumptions
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET LANDSCAPE
- 4.1 Market Overview
- 4.2 Market Drivers
- 4.2.1 Accelerated cloud-first digital transformation
- 4.2.2 IT-OT security convergence across critical infrastructure
- 4.2.3 Zero-trust architecture mandates for hybrid workforce
- 4.2.4 Surge in cyber-insurance underwriting requirements
- 4.2.5 Digital-sovereignty regulations driving localised security stacks
- 4.2.6 Timelines for quantum-ready cryptography migration
- 4.3 Market Restraints
- 4.3.1 Cyber-security talent deficit and wage inflation
- 4.3.2 Integration complexity with legacy infrastructure
- 4.3.3 API-sprawl expanding attack-surface complexity
- 4.3.4 SOC alert-fatigue and false-positive overload limiting ROI
- 4.4 Value Chain Analysis
- 4.5 Evaluation of Critical Regulatory Framework
- 4.6 Impact Assessment of Key Stakeholders
- 4.7 Technological Outlook
- 4.8 Porter's Five Forces Analysis
- 4.8.1 Bargaining Power of Suppliers
- 4.8.2 Bargaining Power of Consumers
- 4.8.3 Threat of New Entrants
- 4.8.4 Threat of Substitutes
- 4.8.5 Intensity of Competitive Rivalry
- 4.9 Key Use Cased and Case Studies
- 4.10 Analysis of Pricing and Pricing Model
- 4.11 Cybersecurity Training Trends
- 4.12 Impact of Macro-economic Factors
5 MARKET SIZE AND GROWTH FORECASTS (VALUE)
- 5.1 By Offering
- 5.1.1 Solutions
- 5.1.1.1 Application Security
- 5.1.1.2 Cloud Security
- 5.1.1.3 Data Security
- 5.1.1.4 Identity and Access Management
- 5.1.1.5 Infrastructure Protection
- 5.1.1.6 Integrated Risk Management
- 5.1.1.7 Network Security
- 5.1.1.8 End-point Security
- 5.1.2 Services
- 5.1.2.1 Professional Services
- 5.1.2.2 Managed Services
- 5.1.1 Solutions
- 5.2 By Deployment Mode
- 5.2.1 Cloud
- 5.2.2 On-Premise
- 5.3 By End-user Industry
- 5.3.1 BFSI
- 5.3.2 Healthcare
- 5.3.3 IT and Telecom
- 5.3.4 Industrial and Defense
- 5.3.5 Retail and E-commerce
- 5.3.6 Energy and Utilities
- 5.3.7 Manufacturing
- 5.3.8 Others
- 5.4 By End-user Enterprise Size
- 5.4.1 Large Enterprises
- 5.4.2 Small and Medium Enterprises (SMEs)
- 5.5 By Geography
- 5.5.1 North America
- 5.5.1.1 United States
- 5.5.1.2 Canada
- 5.5.1.3 Mexico
- 5.5.2 South America
- 5.5.2.1 Brazil
- 5.5.2.2 Argentina
- 5.5.2.3 Rest of South America
- 5.5.3 Europe
- 5.5.3.1 Germany
- 5.5.3.2 United Kingdom
- 5.5.3.3 France
- 5.5.3.4 Italy
- 5.5.3.5 Spain
- 5.5.3.6 Russia
- 5.5.3.7 Rest of Europe
- 5.5.4 Asia-Pacific
- 5.5.4.1 China
- 5.5.4.2 Japan
- 5.5.4.3 India
- 5.5.4.4 South Korea
- 5.5.4.5 Australia and New Zealand
- 5.5.4.6 Rest of Asia-Pacific
- 5.5.5 Middle East and Africa
- 5.5.5.1 Middle East
- 5.5.5.1.1 Saudi Arabia
- 5.5.5.1.2 United Arab Emirates
- 5.5.5.1.3 Turkey
- 5.5.5.1.4 Rest of Middle East
- 5.5.5.2 Africa
- 5.5.5.2.1 South Africa
- 5.5.5.2.2 Nigeria
- 5.5.5.2.3 Egypt
- 5.5.5.2.4 Rest of Africa
- 5.5.5.1 Middle East
- 5.5.1 North America
6 COMPETITIVE LANDSCAPE
- 6.1 Market Concentration
- 6.2 Strategic Moves
- 6.3 Market Share Analysis
- 6.4 Company Profiles (includes Global level Overview, Market level overview, Core Segments, Financials as available, Strategic Information, Market Rank/Share for key companies, Products and Services, and Recent Developments)
- 6.4.1 IBM Corporation
- 6.4.2 Microsoft Corporation
- 6.4.3 Cisco Systems, Inc.
- 6.4.4 Palo Alto Networks, Inc.
- 6.4.5 Fortinet, Inc.
- 6.4.6 Check Point Software Technologies Ltd.
- 6.4.7 CrowdStrike Holdings, Inc.
- 6.4.8 Trend Micro Incorporated
- 6.4.9 Zscaler, Inc.
- 6.4.10 Okta, Inc.
- 6.4.11 Gen Digital Inc. (formerly NortonLifeLock Inc.)
- 6.4.12 Sophos Limited
- 6.4.13 Proofpoint, Inc.
- 6.4.14 McAfee LLC
- 6.4.15 Darktrace plc
- 6.4.16 Rapid7, Inc.
- 6.4.17 SentinelOne, Inc.
- 6.4.18 Imperva, Inc.
- 6.4.19 Qualys, Inc.
- 6.4.20 Trellix Holdings LLC
- 6.4.21 Splunk Inc.
- 6.4.22 Elastic N.V.
- 6.4.23 Akamai Technologies, Inc.
- 6.4.24 Broadcom Inc. (Symantec Enterprise Division)
- 6.4.25 VMware, Inc.
- 6.4.26 Cybereason
- 6.4.27 Ivanti, Inc.
- 6.4.28 Tenable Holdings, Inc.
- 6.4.29 CyberArk Software Ltd.
7 MARKET OPPORTUNITIES AND FUTURE TRENDS
- 7.1 White-space and Unmet-need Assessment



