 |
市場調查報告書
商品編碼
1958437
汽車網路安全市場(至 2040 年):依組件、形式、安全類型、車輛類型、應用、地區和主要參與者劃分的行業趨勢和全球預測Automotive Cybersecurity Market, till 2040: Distribution by Type of Component, Type of Form, Type of Security, Type of Vehicle, Application, Geographical Regions, and Key Players: Industry Trends and Global Forecasts |
||||||
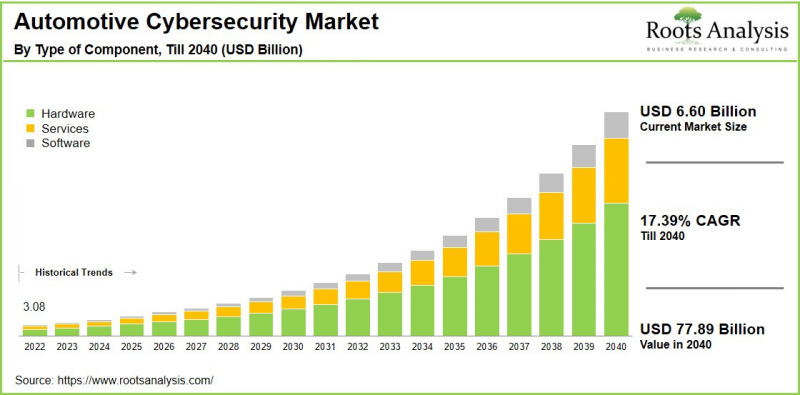
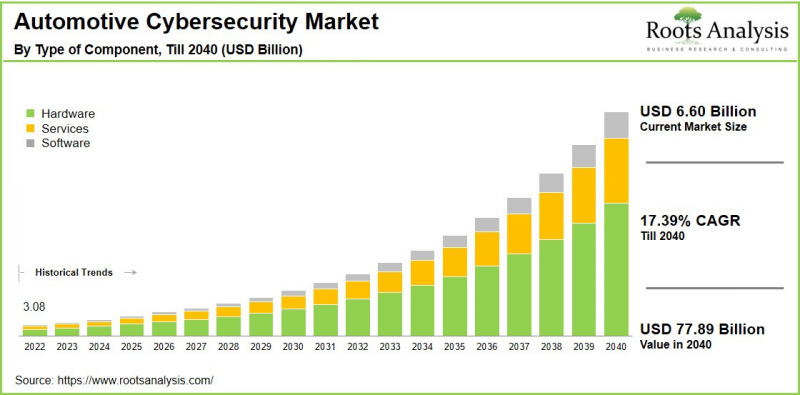
全球汽車網路安全市場預計將從目前的 66 億美元成長到 2040 年的 623.1 億美元,預測期內複合年增長率 (CAGR) 為 17.39%。
汽車網路安全是指保護車輛電子系統、通訊網路和資料免受未經授權存取的技術、流程和實務。隨著現代汽車發展成為具有自動駕駛功能、空中升級 (OTA) 和車聯網 (V2X) 系統的先進“駕駛電腦”,保護連網汽車免受網路威脅(包括保護電子控制單元 (ECU)、車載網路、軟體和資料免受未經授權的存取、篡改和損壞)至關重要。 包含安全設計在內的全生命週期方法可確保強大的防禦能力,並符合 ISO/SAE 21434 等業界標準。
由於自動駕駛、電氣化和軟體定義車輛等車輛數位化趨勢,汽車網路安全市場正在快速擴張。這些趨勢透過遠端資訊處理、空中下載 (OTA) 更新和後端基礎設施擴大了攻擊面。此外,Wi-Fi 和 5G 上的 API 漏洞等威脅的增加,凸顯了基於人工智慧的防禦技術和全產業協作的必要性。因此,預計汽車網路安全市場在預測期內將顯著成長。
推動汽車網路安全市場成長的關鍵因素
推動汽車網路安全市場成長的主要因素是連網和自動駕駛汽車的快速普及。這些車輛整合了空中升級、V2X 通訊和人工智慧驅動系統等先進功能,大大擴展了網路攻擊的攻擊面。此外,ISO/SAE 21434 和 UNECE WP.29 等嚴格的監管要求要求原始設備製造商 (OEM) 和供應商在車輛的整個生命週期中融入安全措施,從而推動了對合規解決方案的需求。此外,針對車載網路的網路安全事件的增加以及消費者對個人資料保護風險意識的提高也在加速市場普及。此外,向軟體定義車輛 (SDV) 的轉變以及電氣化架構的進步進一步加劇了安全漏洞,促使人們增加對先進威脅偵測技術的投資。
汽車網路安全市場:主要市場區隔
依元件
- 硬體
- 軟體
- 服務
依形式
- 外部安全
- 車載安全
依安全性類型
- 應用
- 雲
- 數據
- 終端
- 硬體
- 網絡
- 無線網路
- 其他
依車輛類型
- 電動車
- 燃油汽車
依應用
- 進階駕駛輔助系統 (ADAS) 與安全系統
- 車身控制與舒適系統
- 通訊管道
- 資訊娛樂系統
- 車載診斷系統
- 動力系統
- 遠端資訊處理系統
- 其他
依地區
- 北美
- 美國
- 加拿大
- 墨西哥
- 北美其他地區
- 歐洲
- 奧地利
- 比利時
- 丹麥
- 法國
- 德國
- 愛爾蘭
- 義大利
- 荷蘭
- 挪威
- 俄羅斯
- 西班牙
- 瑞典
- 瑞士
- 英國
- 歐洲其他地區
- 亞洲太平洋地區
- 澳大利亞
- 中國
- 印度
- 日本
- 紐西蘭
- 新加坡
- 韓國 亞太其他地區
- 拉丁美洲
- 巴西
- 智利
- 哥倫比亞
- 委內瑞拉
- 拉丁美洲其他地區
- 中東和非洲
- 埃及
- 伊朗
- 伊拉克
- 以色列
- 科威特
- 沙烏地阿拉伯
- 阿拉伯聯合大公國
- 中東和非洲其他地區
本報告分析了全球汽車網路安全市場,並提供了市場概覽、背景介紹、市場影響因素分析、市場規模趨勢和預測、依細分市場和地區劃分的詳細分析、競爭格局以及主要公司簡介。
目錄
第一章:專案概述
第二章:研究方法
第三章:市場動態
第四章:宏觀經濟指標
第五章:摘要整理
第六章:引言
第七章:監理環境
第八章:主要公司綜合資料庫
第九章:競爭格局
第十章:市場空白分析
第十一章:公司競爭力分析
第 12 章:新創企業生態系分析
第 13 章:公司簡介
- 章節概述
- 安波福
- Argus Cyber Security(原 PlaxidityX)
- 黑莓
- 博通
- 大陸航空
- 電裝
- GuardKnox 網路技術
- 哈曼國際
- 霍尼韋爾
- 卡蘭巴安全
- 恩智浦半導體
- 羅伯特·博世
- 安全乘車技術
- 延齡草安全
- 上游安全
- 向量資訊學
第十四章 大趨勢分析
第十五章 未滿足需求分析
第十六章:專利分析
第十七章:近期趨勢
第十八章:全球汽車網路安全市場
第十九章:依組件劃分的市場機會
第二十章:依配置劃分的市場機會
第二十一章:依安全類型劃分的市場機會
第二十二章:依車輛類型劃分的市場機會
第二十三章:依應用劃分的市場機會
章節第24章:北美汽車網路安全市場機會
第25章:歐洲汽車網路安全市場機會
第26章:亞太地區汽車網路安全市場機會
第27章:拉丁美洲汽車網路安全市場機會
第28章:中東與非洲汽車網路安全市場機會
第29章:市場集中度分析:主要參與者分佈
第30章:相鄰市場分析
第31章:關鍵制勝策略
第32章:波特五力分析
第33章: SWOT 分析
第 34 章:價值鏈分析
第 35 章:ROOTS 策略建議
第 36 章:來自一手研究的洞見
第 37 章:報告結論
第 38 章:表格資料
第 39 章:公司與組織清單
Automotive Cybersecurity Market Outlook
As per Roots Analysis, the global automotive cybersecurity market size is estimated to grow from USD 6.60 billion in current year to USD 62.31 billion by 2040, at a CAGR of 17.39% during the forecast period, till 2040.
Automotive cybersecurity refers to the technologies, processes, and practices that safeguard vehicle electronic systems, communication networks, and data against unauthorized access. It safeguards connected vehicles against cyber threats by securing electronic control units (ECUs), in-vehicle networks, software, and data from unauthorized access, manipulation, and damage. This protection is essential as modern cars evolve into advanced "driving computers" equipped with autonomous driving capabilities, over-the-air (OTA) updates, and vehicle-to-everything (V2X) communication systems. A comprehensive lifecycle approach, such as security by design, ensures robust defenses, complemented by adherence to industry standards like ISO / SAE 21434.
The automotive cybersecurity market is expanding rapidly due to vehicle digitization trends, including autonomous driving, electrification, and software-defined vehicles, which increase attack surfaces through telematics, over-the-air (OTA) updates, and backend infrastructure. Further, rising threats, such as API vulnerabilities over Wi-Fi and 5G, underscore the demand for AI-powered defenses and collaborative industry efforts. Overall, considering the above-mentioned factors, the automotive cybersecurity market is expected to grow significantly during the forecast period.
Strategic Insights for Senior Leaders
Key Drivers Propelling Growth of Automotive Cybersecurity Market
Key drivers propelling the growth of the automotive cybersecurity market include the rapid use of connected and autonomous vehicles, which integrate advanced features like over-the-air updates, V2X communication, and AI-driven systems. This exponentially expands the attack surface for cyber threats. Stringent regulatory mandates, such as ISO/SAE 21434 and UNECE WP.29, compel original equipment manufacturers (OEMs) and suppliers to embed security throughout the vehicle lifecycle, driving demand for compliant solutions. Escalating cyber incidents targeting vehicle networks, coupled with rising consumer awareness of data privacy risks, further accelerate adoption. Additionally, the shift toward software-defined vehicles and electric architectures heightens vulnerability, spurring investments in advanced threat detection.
Strategic Approaches for Capturing Automotive Cybersecurity Market Share
The automotive cybersecurity market features a dynamic competitive landscape including established automotive suppliers and specialized cybersecurity firms, both advancing innovation and regulatory compliance. The firm "Continental" stands out with its end-to-end cybersecurity portfolio, encompassing intrusion detection and prevention systems alongside secure gateway solutions customized for OEMs like BMW and Ford.
Robert Bosch leverages its extensive vehicle electronics expertise to dominate cyber threat protection, embedding cryptographic security. Aptiv sets itself apart via advanced V2X security protocols and AI-powered threat detection, bolstering cybersecurity for connected and autonomous vehicles.
Leading players, including Harman International and Karamba Security, prioritize multi-layered defense mechanisms amid stringent global regulations, while fostering collaborative ecosystems with semiconductor providers and cybersecurity software developers.
Automotive Cybersecurity Evolution: Emerging Trends in the Industry
Emerging trends in the automotive cybersecurity industry are reshaping the sector amid the rise of software-defined vehicles and heightened connectivity. AI-driven threat intelligence and predictive analytics enable real-time anomaly detection and automated response, outpacing traditional rule-based systems. Zero-trust architectures and secure-by-design principles gain traction, enforcing continuous verification across ECUs, V2X networks, and OTA update pipelines. Quantum-resistant cryptography addresses future-proofing against evolving computational threats, while blockchain integration enhances supply chain integrity and software provenance. Further, collaborative ecosystems, including OEM-supplier consortia and standards like ISO/SAE 21434 updates, accelerate adoption of composable security platforms tailored for Level 4/5 autonomy.
Regional Analysis: Asia-Pacific Lead the Automotive Cybersecurity Market
According to our analysis, in the current year, the automotive cybersecurity market in Asia-Pacific captures the largest share. This is due to its dominant position in global vehicle production, particularly in China, Japan, and South Korea, where surging demand for connected cars, electric vehicles, and advanced driver-assistance systems (ADAS) amplifies cybersecurity needs. This growth is further supported by government initiatives promoting intelligent transportation infrastructure, coupled with stringent regulations. Moreover, rapid 5G deployment, expansive semiconductor networks, and large-scale exports of software-defined vehicles further accelerates the adoption of cybersecurity.
Key Challenges in Automotive Cybersecurity Market
The second-life EV battery market faces several key challenges that could impede widespread adoption. One of the primary challenges include the complexity of interconnected supply chains, which create multiple vulnerability entry points across diverse components and stakeholders. Increased connectivity through Wi-Fi, Bluetooth, cellular networks, and OTA updates vastly expands the attack surface, while escalating software complexity in software-defined and autonomous vehicles. High implementation costs burden smaller manufacturers, along with a critical talent shortage for professionals skilled in automotive cybersecurity. Further, regulatory compliance with evolving standards like UNECE WP.29 adds operational complexity, alongside data privacy concerns from vast personal data collection and inadequate incident response planning.
Automotive Cybersecurity Market: Key Market Segmentation
By Type of Component
- Hardware
- Software
- Services
By Type of Form
- External Security
- In-Vehicle Security
By Type of Security
- Application
- Cloud
- Data
- Endpoint
- Hardware
- Network
- Wireless Network
- Others
By Type of Vehicle
- Electric Vehicles
- Fuel-based Vehicles
By Application
- ADAS & Safety Systems
- Body Control & Comfort Systems
- Communication Channels
- Infotainment
- On-Board Diagnostics
- Powertrain
- Telematics
- Others
By Geographical Regions
- North America
- US
- Canada
- Mexico
- Rest of North America
- Europe
- Austria
- Belgium
- Denmark
- France
- Germany
- Ireland
- Italy
- Netherlands
- Norway
- Russia
- Spain
- Sweden
- Switzerland
- UK
- Rest of Europe
- Asia-Pacific
- Australia
- China
- India
- Japan
- New-Zealand
- Singapore
- South Korea
- Rest of Asia-Pacific
- Latin America
- Brazil
- Chile
- Colombia
- Venezuela
- Rest of Latin America
- Middle East and Africa (MEA)
- Egypt
- Iran
- Iraq
- Israel
- Kuwait
- Saudi Arabia
- UAE
- Rest of MEA
Automotive Cybersecurity Market: Report Coverage
The report on the automotive cybersecurity market features insights on various sections, including:
- Market Sizing and Opportunity Analysis: An in-depth analysis of the automotive cybersecurity market, focusing on key market segments, including [A] type of component, [B] type of form, [C] type of security, [D] type of vehicle, [E] application, [F] geographical regions, and [G] key players.
- Competitive Landscape: A comprehensive analysis of the companies engaged in the automotive cybersecurity market, based on several relevant parameters, such as [A] year of establishment, [B] company size, [C] location of headquarters and [D] ownership structure.
- Company Profiles: Elaborate profiles of prominent players engaged in the automotive cybersecurity market, providing details on [A] location of headquarters, [B] company size, [C] company mission, [D] company footprint, [E] management team, [F] contact details, [G] financial information, [H] operating business segments, [I] product / technology portfolio, [J] recent developments, and an informed future outlook.
- Megatrends: An evaluation of ongoing megatrends in the automotive cybersecurity industry.
- Patent Analysis: An insightful analysis of patents filed / granted in the automotive cybersecurity domain, based on relevant parameters, including [A] type of patent, [B] patent publication year, [C] patent age and [D] leading players.
- Recent Developments: An overview of the recent developments made in the automotive cybersecurity market, along with analysis based on relevant parameters, including [A] year of initiative, [B] type of initiative, [C] geographical distribution and [D] most active players.
- Porter's Five Forces Analysis: An analysis of five competitive forces prevailing in the automotive cybersecurity market, including threats of new entrants, bargaining power of buyers, bargaining power of suppliers, threats of substitute products and rivalry among existing competitors.
- SWOT Analysis: An insightful SWOT framework, highlighting the strengths, weaknesses, opportunities and threats in the domain. Additionally, it provides Harvey ball analysis, highlighting the relative impact of each SWOT parameter.
Key Questions Answered in this Report
- What is the current and future market size?
- Who are the leading companies in this market?
- What are the growth drivers that are likely to influence the evolution of this market?
- What are the key partnership and funding trends shaping this industry?
- Which region is likely to grow at higher CAGR till 2040?
- How is the current and future market opportunity likely to be distributed across key market segments?
Reasons to Buy this Report
- Detailed Market Analysis: The report provides a comprehensive market analysis, offering detailed revenue projections of the overall market and its specific sub-segments. This information is valuable to both established market leaders and emerging entrants.
- In-depth Analysis of Trends: Stakeholders can leverage the report to gain a deeper understanding of the competitive dynamics within the market. Each report maps ecosystem activity across partnerships, funding, and patent landscapes to reveal growth hotspots and white spaces in the industry.
- Opinion of Industry Experts: The report features extensive interviews and surveys with key opinion leaders and industry experts to validate market trends mentioned in the report.
- Decision-ready Deliverables: The report offers stakeholders with strategic frameworks (Porter's Five Forces, value chain, SWOT), and complimentary Excel / slide packs with customization support.
Additional Benefits
- Complimentary Dynamic Excel Dashboards for Analytical Modules
- Exclusive 15% Free Content Customization
- Personalized Interactive Report Walkthrough with Our Expert Research Team
- Free Report Updates for Versions Older than 6-12 Months
TABLE OF CONTENTS
1. PROJECT OVERVIEW
- 1.1. Context
- 1.2. Project Objectives
2. RESEARCH METHODOLOGY
- 2.1. Chapter Overview
- 2.2. Research Assumptions
- 2.3. Database Building
- 2.3.1. Data Collection
- 2.3.2. Data Validation
- 2.3.3. Data Analysis
- 2.4. Project Methodology
- 2.4.1. Secondary Research
- 2.4.1.1. Annual Reports
- 2.4.1.2. Academic Research Papers
- 2.4.1.3. Company Websites
- 2.4.1.4. Investor Presentations
- 2.4.1.5. Regulatory Filings
- 2.4.1.6. White Papers
- 2.4.1.7. Industry Publications
- 2.4.1.8. Conferences and Seminars
- 2.4.1.9. Government Portals
- 2.4.1.10. Media and Press Releases
- 2.4.1.11. Newsletters
- 2.4.1.12. Industry Databases
- 2.4.1.13. Roots Proprietary Databases
- 2.4.1.14. Paid Databases and Sources
- 2.4.1.15. Social Media Portals
- 2.4.1.16. Other Secondary Sources
- 2.4.2. Primary Research
- 2.4.2.1. Introduction
- 2.4.2.2. Types
- 2.4.2.2.1. Qualitative
- 2.4.2.2.2. Quantitative
- 2.4.2.3. Advantages
- 2.4.2.4. Techniques
- 2.4.2.4.1. Interviews
- 2.4.2.4.2. Surveys
- 2.4.2.4.3. Focus Groups
- 2.4.2.4.4. Observational Research
- 2.4.2.4.5. Social Media Interactions
- 2.4.2.5. Stakeholders
- 2.4.2.5.1. Company Executives (CXOs)
- 2.4.2.5.2. Board of Directors
- 2.4.2.5.3. Company Presidents and Vice Presidents
- 2.4.2.5.4. Key Opinion Leaders
- 2.4.2.5.5. Research and Development Heads
- 2.4.2.5.6. Technical Experts
- 2.4.2.5.7. Subject Matter Experts
- 2.4.2.5.8. Scientists
- 2.4.2.5.9. Doctors and Other Healthcare Providers
- 2.4.2.6. Ethics and Integrity
- 2.4.2.6.1. Research Ethics
- 2.4.2.6.2. Data Integrity
- 2.4.3. Analytical Tools and Databases
- 2.4.1. Secondary Research
3. MARKET DYNAMICS
- 3.1. Forecast Methodology
- 3.1.1. Top-Down Approach
- 3.1.2. Bottom-Up Approach
- 3.1.3. Hybrid Approach
- 3.2. Market Assessment Framework
- 3.2.1. Total Addressable Market (TAM)
- 3.2.2. Serviceable Addressable Market (SAM)
- 3.2.3. Serviceable Obtainable Market (SOM)
- 3.2.4. Currently Acquired Market (CAM)
- 3.3. Forecasting Tools and Techniques
- 3.3.1. Qualitative Forecasting
- 3.3.2. Correlation
- 3.3.3. Regression
- 3.3.4. Time Series Analysis
- 3.3.5. Extrapolation
- 3.3.6. Convergence
- 3.3.7. Forecast Error Analysis
- 3.3.8. Data Visualization
- 3.3.9. Scenario Planning
- 3.3.10. Sensitivity Analysis
- 3.4. Key Considerations
- 3.4.1. Demographics
- 3.4.2. Market Access
- 3.4.3. Reimbursement Scenarios
- 3.4.4. Industry Consolidation
- 3.5. Robust Quality Control
- 3.6. Key Market Segmentations
- 3.7. Limitations
4. MACRO-ECONOMIC INDICATORS
- 4.1. Chapter Overview
- 4.2. Market Dynamics
- 4.2.1. Time Period
- 4.2.1.1. Historical Trends
- 4.2.1.2. Current and Forecasted Estimates
- 4.2.2. Currency Coverage
- 4.2.2.1. Overview of Major Currencies Affecting the Market
- 4.2.2.2. Impact of Currency Fluctuations on the Industry
- 4.2.3. Foreign Exchange Impact
- 4.2.3.1. Evaluation of Foreign Exchange Rates and Their Impact on Market
- 4.2.3.2. Strategies for Mitigating Foreign Exchange Risk
- 4.2.4. Recession
- 4.2.4.1. Historical Analysis of Past Recessions and Lessons Learnt
- 4.2.4.2. Assessment of Current Economic Conditions and Potential Impact on the Market
- 4.2.5. Inflation
- 4.2.5.1. Measurement and Analysis of Inflationary Pressures in the Economy
- 4.2.5.2. Potential Impact of Inflation on the Market Evolution
- 4.2.6. Interest Rates
- 4.2.6.1. Overview of Interest Rates and Their Impact on the Market
- 4.2.6.2. Strategies for Managing Interest Rate Risk
- 4.2.7. Commodity Flow Analysis
- 4.2.7.1. Type of Commodity
- 4.2.7.2. Origins and Destinations
- 4.2.7.3. Values and Weights
- 4.2.7.4. Modes of Transportation
- 4.2.8. Global Trade Dynamics
- 4.2.8.1. Import Scenario
- 4.2.8.2. Export Scenario
- 4.2.9. War Impact Analysis
- 4.2.9.1. Russian-Ukraine War
- 4.2.9.2. Israel-Hamas War
- 4.2.10. COVID Impact / Related Factors
- 4.2.10.1. Global Economic Impact
- 4.2.10.2. Industry-specific Impact
- 4.2.10.3. Government Response and Stimulus Measures
- 4.2.10.4. Future Outlook and Adaptation Strategies
- 4.2.11. Other Indicators
- 4.2.11.1. Fiscal Policy
- 4.2.11.2. Consumer Spending
- 4.2.11.3. Gross Domestic Product (GDP)
- 4.2.11.4. Employment
- 4.2.11.5. Taxes
- 4.2.11.6. R&D Innovation
- 4.2.11.7. Stock Market Performance
- 4.2.11.8. Supply Chain
- 4.2.11.9. Cross-Border Dynamics
- 4.2.1. Time Period
- 4.3. Concluding Remarks
5. EXECUTIVE SUMMARY
6. INTRODUCTION
- 6.1. Overview of Automotive Cybersecurity market
- 6.2. Application for Automotive Cybersecurity
- 6.3. Advantages of Automotive cybersecurity
- 6.4. Challenges Associated with Automotive cybersecurity
- 6.5. Future Perspective
7. REGULATORY SCENARIO
8. COMPREHENSIVE DATABASE OF LEADING PLAYERS
9. COMPETITIVE LANDSCAPE
- 9.1. Chapter Overview
- 9.2. Automotive Cybersecurity market: Overall Market Landscape
- 9.2.1. Analysis by Year of Establishment
- 9.2.2. Analysis by Company Size
- 9.2.3. Analysis by Location of Headquarters
- 9.2.4. Analysis by Type of Company
- 9.2.5. Analysis by Application
- 9.2.6. Analysis by End Use Industry
- 9.3. Key Findings
10. WHITE SPACE ANALYSIS
11. COMPANY COMPETITIVENESS ANALYSIS
12. STARTUP ECOSYSTEM ANALYSIS
- 12.1. Automotive Cybersecurity market: Startup Ecosystem Analysis
- 12.1.1. Analysis by Year of Establishment
- 12.1.2. Analysis by Company Size
- 12.1.3. Analysis by Location of Headquarters
- 12.1.4. Analysis by Ownership Type
- 12.1.5. Analysis by Application
- 12.1.6. Analysis by End Use Sector
- 12.2. Key Findings
13. COMPANY PROFILES
- 13.1. Chapter Overview
- 13.2. Aptiv *
- 13.2.1. Company Overview
- 13.2.2. Company Mission
- 13.2.3. Company Footprint
- 13.2.4. Management Team
- 13.2.5. Contact Details
- 13.2.6. Financial Performance
- 13.2.7. Operating Business Segments
- 13.2.8. Service / Product Portfolio (project specific)
- 13.2.9. MOAT Analysis
- 13.2.10. Recent Developments and Future Outlook
- similar details are presented for other below mentioned companies based on information in the public domain
- 13.3. Argus Cyber Security (formerly known as PlaxidityX)
- 13.4. BlackBerry
- 13.5. Broadcom
- 13.6. Continental
- 13.7. Denso
- 13.8. GuardKnox Cyber-Technologies
- 13.9. Harman International
- 13.10. Honeywell
- 13.11. Karamba Security
- 13.12. NXP Semiconductors
- 13.13. Robert Bosch
- 13.14. SafeRide Technologies
- 13.15. Trillium Secure
- 13.16. Upstream Security
- 13.17. Vector Informatik
14. MEGA TRENDS ANALYSIS
15. UNMET NEED ANALYSIS
16. PATENT ANALYSIS
17. RECENT DEVELOPMENTS
- 17.1. Chapter Overview
- 17.2. Recent Funding
- 17.3. Recent Partnerships
- 17.4. Other Recent Initiatives
18. GLOBAL AUTOMOTIVE CYBERSECURITY MARKET
- 18.1. Chapter Overview
- 18.2. Key Assumptions and Methodology
- 18.3. Trends Disruption Impacting Market
- 18.4. Demand Side Trends
- 18.5. Supply Side Trends
- 18.6. Global Automotive Cybersecurity Market, Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 18.7. Multivariate Scenario Analysis
- 18.7.1. Conservative Scenario
- 18.7.2. Optimistic Scenario
- 18.8. Investment Feasibility Index
- 18.9. Key Market Segmentations
19. MARKET OPPORTUNITIES BASED ON COMPONENT
- 19.1. Chapter Overview
- 19.2. Key Assumptions and Methodology
- 19.3. Revenue Shift Analysis
- 19.4. Market Movement Analysis
- 19.5. Penetration-Growth (P-G) Matrix
- 19.6. Automotive Cybersecurity Market for Hardware: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 19.7. Automotive Cybersecurity Market for Software: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 19.8. Automotive Cybersecurity Market for Services: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 19.9. Data Triangulation and Validation
- 19.9.1. Secondary Sources
- 19.9.2. Primary Sources
- 19.9.3. Statistical Modeling
20. MARKET OPPORTUNITIES BASED ON TYPE OF FORM
- 20.1. Chapter Overview
- 20.2. Key Assumptions and Methodology
- 20.3. Revenue Shift Analysis
- 20.4. Market Movement Analysis
- 20.5. Penetration-Growth (P-G) Matrix
- 20.6. Automotive Cybersecurity Market for External Security: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 20.7. Automotive Cybersecurity Market for In-Vehicle Security: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 20.8. Data Triangulation and Validation
- 20.8.1. Secondary Sources
- 20.8.2. Primary Sources
- 20.8.3. Statistical Modeling
21. MARKET OPPORTUNITIES BASED ON TYPE OF SECURITY
- 21.1. Chapter Overview
- 21.2. Key Assumptions and Methodology
- 21.3. Revenue Shift Analysis
- 21.4. Market Movement Analysis
- 21.5. Penetration-Growth (P-G) Matrix
- 21.6. Automotive Cybersecurity Market for Application: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.7. Automotive Cybersecurity Market for Cloud: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.8. Automotive Cybersecurity Market for Data: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.9. Automotive Cybersecurity Market for Endpoint: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.10. Automotive Cybersecurity Market for Hardware: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.11. Automotive Cybersecurity Market for Network: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.12. Automotive Cybersecurity Market for Wireless Network: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.13. Automotive Cybersecurity Market for Others: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 21.14. Data Triangulation and Validation
- 21.14.1. Secondary Sources
- 21.14.2. Primary Sources
- 21.14.3. Statistical Modeling
22. MARKET OPPORTUNITIES BASED ON TYPE OF VEHICLE
- 22.1. Chapter Overview
- 22.2. Key Assumptions and Methodology
- 22.3. Revenue Shift Analysis
- 22.4. Market Movement Analysis
- 22.5. Penetration-Growth (P-G) Matrix
- 22.6. Automotive Cybersecurity Market for Electric Vehicles: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 22.7. Automotive Cybersecurity Market for Fuel-based Vehicles: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 22.8. Data Triangulation and Validation
- 22.8.1. Secondary Sources
- 22.8.2. Primary Sources
- 22.8.3. Statistical Modeling
23. MARKET OPPORTUNITIES BASED ON APPLICATION
- 23.1. Chapter Overview
- 23.2. Key Assumptions and Methodology
- 23.3. Revenue Shift Analysis
- 23.4. Market Movement Analysis
- 23.5. Penetration-Growth (P-G) Matrix
- 23.6. Automotive Cybersecurity Market for ADAS & Safety Systems: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.7. Automotive Cybersecurity Market for Body Control & Comfort Systems: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.8. Automotive Cybersecurity Market for Communication Channels: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.9. Automotive Cybersecurity Market for Infotainment: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.10. Automotive Cybersecurity Market for On-Board Diagnostics: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.11. Automotive Cybersecurity Market for Powertrain: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.12. Automotive Cybersecurity Market for Telematics: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.13. Automotive Cybersecurity Market for Others: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 23.14. Data Triangulation and Validation
- 23.14.1. Secondary Sources
- 23.14.2. Primary Sources
- 23.14.3. Statistical Modeling
24. MARKET OPPORTUNITIES FOR AUTOMOTIVE CYBERSECURITY IN NORTH AMERICA
- 24.1. Chapter Overview
- 24.2. Key Assumptions and Methodology
- 24.3. Revenue Shift Analysis
- 24.4. Market Movement Analysis
- 24.5. Penetration-Growth (P-G) Matrix
- 24.6. Automotive Cybersecurity Market in North America: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 24.6.1. Automotive Cybersecurity Market in the US: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 24.6.2. Automotive Cybersecurity Market in Canada: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 24.6.3. Automotive Cybersecurity Market in Mexico: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 24.6.4. Automotive Cybersecurity Market in Rest of North America: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 24.7. Data Triangulation and Validation
25. MARKET OPPORTUNITIES FOR AUTOMOTIVE CYBERSECURITY IN EUROPE
- 25.1. Chapter Overview
- 25.2. Key Assumptions and Methodology
- 25.3. Revenue Shift Analysis
- 25.4. Market Movement Analysis
- 25.5. Penetration-Growth (P-G) Matrix
- 25.6. Automotive Cybersecurity Market in Europe: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.1. Automotive Cybersecurity Market in Austria: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.2. Automotive Cybersecurity Market in Belgium: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.3. Automotive Cybersecurity Market in Denmark: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.4. Automotive Cybersecurity Market in France: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.5. Automotive Cybersecurity Market in Germany: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.6. Automotive Cybersecurity Market in Ireland: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.7. Automotive Cybersecurity Market in Italy: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.8. Automotive Cybersecurity Market in the Netherlands: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.9. Automotive Cybersecurity Market in Norway: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.10. Automotive Cybersecurity Market in Russia: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.11. Automotive Cybersecurity Market in Spain: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.12. Automotive Cybersecurity Market in Sweden: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.13. Automotive Cybersecurity Market in Switzerland: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.14. Automotive Cybersecurity Market in the UK: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.6.15. Automotive Cybersecurity Market in Rest of Europe: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 25.7. Data Triangulation and Validation
26. MARKET OPPORTUNITIES FOR AUTOMOTIVE CYBERSECURITY IN ASIA-PACIFIC
- 26.1. Chapter Overview
- 26.2. Key Assumptions and Methodology
- 26.3. Revenue Shift Analysis
- 26.4. Market Movement Analysis
- 26.5. Penetration-Growth (P-G) Matrix
- 26.6. Automotive Cybersecurity Market in Asia-Pacific: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 26.6.1. Automotive Cybersecurity Market in China: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 26.6.2. Automotive Cybersecurity Market in India: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 26.6.3. Automotive Cybersecurity Market in Japan: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 26.6.4. Automotive Cybersecurity Market in Singapore: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 26.6.5. Automotive Cybersecurity Market in South Korea: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 26.6.6. Automotive Cybersecurity Market in Rest of Asia-Pacific: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 26.7. Data Triangulation and Validation
27. MARKET OPPORTUNITIES FOR AUTOMOTIVE CYBERSECURITY IN LATIN AMERICA
- 27.1. Chapter Overview
- 27.2. Key Assumptions and Methodology
- 27.3. Revenue Shift Analysis
- 27.4. Market Movement Analysis
- 27.5. Penetration-Growth (P-G) Matrix
- 27.6. Automotive Cybersecurity Market in Latin America: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 27.6.1. Automotive Cybersecurity Market in Argentina: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 27.6.2. Automotive Cybersecurity Market in Brazil: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 27.6.3. Automotive Cybersecurity Market in Chile: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 27.6.4. Automotive Cybersecurity Market in Colombia Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 27.6.5. Automotive Cybersecurity Market in Venezuela: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 27.6.6. Automotive Cybersecurity Market in Rest of Latin America: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 27.7. Data Triangulation and Validation
28. MARKET OPPORTUNITIES FOR AUTOMOTIVE CYBERSECURITY IN MIDDLE EAST AND AFRICA (MEA)
- 28.1. Chapter Overview
- 28.2. Key Assumptions and Methodology
- 28.3. Revenue Shift Analysis
- 28.4. Market Movement Analysis
- 28.5. Penetration-Growth (P-G) Matrix
- 28.6. Automotive Cybersecurity Market in Middle East and Africa (MEA): Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.6.1. Automotive Cybersecurity Market in Egypt: Historical Trends (Since 2022) and Forecasted Estimates (Till 205)
- 28.6.2. Automotive Cybersecurity Market in Iran: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.6.3. Automotive Cybersecurity Market in Iraq: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.6.4. Automotive Cybersecurity Market in Israel: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.6.5. Automotive Cybersecurity Market in Kuwait: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.6.6. Automotive Cybersecurity Market in Saudi Arabia: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.6.7. Automotive Cybersecurity Market in United Arab Emirates (UAE): Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.6.8. Automotive Cybersecurity Market in Rest of MEA: Historical Trends (Since 2022) and Forecasted Estimates (Till 2040)
- 28.7. Data Triangulation and Validation
29. MARKET CONCENTRATION ANALYSIS: DISTRIBUTION BY LEADING PLAYERS
30. ADJACENT MARKET ANALYSIS
31. KEY WINNING STRATEGIES
32. PORTER'S FIVE FORCES ANALYSIS
33. SWOT ANALYSIS
34. VALUE CHAIN ANALYSIS
35. ROOTS STRATEGIC RECOMMENDATIONS
- 35.1. Chapter Overview
- 35.2. Key Business-related Strategies
- 35.2.1. Research & Development
- 35.2.2. Product Manufacturing
- 35.2.3. Commercialization / Go-to-Market
- 35.2.4. Sales and Marketing
- 35.3. Key Operations-related Strategies
- 35.3.1. Risk Management
- 35.3.2. Workforce
- 35.3.3. Finance
- 35.3.4. Others









