 |
市場調查報告書
商品編碼
1687447
欺敵技術:市場佔有率分析、產業趨勢與統計、成長預測(2025-2030 年)Deception Technology - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2025 - 2030) |
||||||
※ 本網頁內容可能與最新版本有所差異。詳細情況請與我們聯繫。
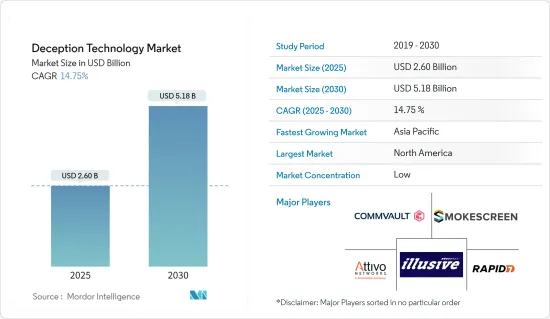
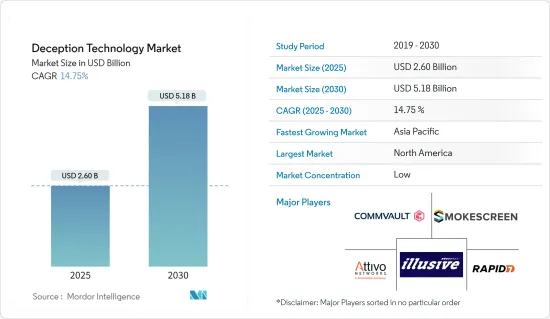
2025 年欺敵技術市場規模預估為 26 億美元,預計到 2030 年將達到 51.8 億美元,預測期內(2025-2030 年)的複合年成長率為 14.75%。
主要亮點
- 欺敵技術是一種用於偵測和防禦針對性攻擊的先進安全解決方案。欺騙是透過故意干擾、虛假反應、誤導和偽造來實現的。
- 網路威脅程度的不斷提高增加了偵測和減輕已經滲透到您的網路的高階風險的需要。這推動了欺敵技術的採用。
- 目前的安全工具可以有效地標記異常,但其影響和潛在風險需要更加清晰。這些工具會產生大量警報,其中許多警報對於安全團隊來說只是浪費時間進行調查。在必須解決真正威脅的同時,評估這些虛假威脅卻浪費了資源。透過改變攻擊的不對稱性,欺騙技術使安全團隊能夠專注於其網路的真正威脅。這樣的場景正在幫助欺敵技術在預測期內獲得發展動力。
- 許多欺騙解決方案的核心都是人工智慧和機器學習(ML)。這些功能可使欺騙技術保持不斷動態,並使他們無需不斷創建新的欺騙宣傳活動,從而有助於減少營運開銷並減少對安全團隊的影響。
- 在 COVID-19 疫情期間,影響個人、企業和組織的網路攻擊激增。結果,一些受影響的公司正在投資升級其過時的系統,從而助長了欺騙技術市場。例如,美國國防安全保障部已就與疫情有關的新興網路犯罪分子和高階持續威脅團體發出警告。國際刑事警察組織(INTERPOL)就故意針對醫療設施的犯罪者發出警告。
欺敵技術的市場趨勢
網路安全預計將高速成長
- 零時差攻擊是一種有針對性的攻擊,攻擊者發現軟體中的漏洞,然後與其他駭客一起利用漏洞,直到組織意識到這一點。零時差攻擊最初沒有留下任何偵測機會。
- 2021年,Mandiant威脅情報發現了80個零日漏洞。利用零日漏洞的主要行為者仍然是由中國團體領導的國家支持的組織。我們也發現,出於經濟動機而利用零日漏洞的行為者比例顯著增加,前年發現的利用零日漏洞的行為者中,有近三分之一是出於經濟動機。
- 此外,威脅行為者最常利用微軟、蘋果和谷歌產品中的零日漏洞,這反映了這些製造商的受歡迎程度。過去一年中,零時差漏洞利用顯著增加,利用這些漏洞的行為者也更加多樣化,這擴大了幾乎所有行業和地區的公司的風險組合,特別是那些依賴這些廣泛使用的系統的公司。
- 研究表明,零時差攻擊的增加是由多種因素造成的。例如,雲端託管、行動和物聯網 (IoT) 技術的持續採用正在增加網際網路連接系統和設備的數量和複雜性。換句話說,軟體越多,軟體缺陷就越多。這一趨勢也受到了漏洞仲介行業的興起的推動,私營部門組織、研究人員和威脅組織向零日漏洞研究和開發投入了更多資源。
- 隨著零時差攻擊和 APT 的興起,世界各地的組織都在部署欺敵技術,以便儘早發現攻擊並最大限度地減少對敏感資料的影響。因此,如圖所示,預計預測期內資料外洩成本的增加將推動欺敵技術市場的發展。
北美預計將佔據主要市場佔有率
- 由於金融服務、醫療保健和政府機構等受到嚴格監管的行業擴大採用欺敵技術解決方案,預計北美地區將佔據全球欺敵技術市場的很大佔有率。美國幾個州,最著名的是《加州消費者隱私法案》(CCPA),已經頒布了隱私法,大大推動了終端用戶產業對欺騙技術解決方案的需求。
- 加州通過了獨立於《加州消費者隱私法案》的立法,以解決物聯網設備的預設密碼和物聯網漏洞問題。為此,國家網路安全和通訊整合中心 (NCCIC) 推出了技術警報 (TA),為 MSP 客戶網路和系統管理員提供資訊和指導,以偵測其網路和系統上的惡意活動並降低相關風險。
- 本 TA 概述了 APT 參與者在 MSP 網路環境中使用的 TTP、緩解提案以及報告事件的詳細資訊。適當基礎設施的高可用性、大量全球金融機構的存在、高頻率的網路攻擊以及技術的不斷採用,預計將推動北美地區欺騙技術市場的成長。
- 推動北美欺騙技術成長的關鍵趨勢包括智慧型手機設備的興起以及產生包含有價值資訊的樣本資料的社交應用程式的日益普及。這大大增加了網路威脅的風險。
- 此外,知名市場供應商的存在以及各個組織中資料量的增加正在推動該地區對欺騙技術解決方案的需求。此外,各個終端用戶領域對 5G、AI、雲端和物聯網等先進技術的早期採用正在迅速推動對欺敵技術解決方案的需求。
欺敵技術產業概況
欺敵技術市場高度分散,主要公司包括 Illusive Networks、Commvault Systems Inc.、Smokescreen Technologies Pvt.有限公司、Attivo Networks Inc. (Sentinelone Inc.) 和 Rapid7 LLC。市場參與者正在採用夥伴關係、創新、合併和收購等策略來增強其產品供應並獲得永續的競爭優勢。
2023年2月,Rapid7與南佛羅裡達大學(USF)宣布成立網路威脅情報研究所,以支持四所學院的教師和學生進行跨領域研究活動。
2022 年 9 月,Commvault 宣布全面推出 Metallic ThreatWise,這是一種警報系統,可在未知威脅和零時差威脅發生之前發現它們,從而最大限度地減少對受損資料和業務的影響。
其他福利:
- Excel 格式的市場預測 (ME) 表
- 3 個月的分析師支持
目錄
第 1 章 簡介
- 研究假設和市場定義
- 研究範圍
第2章調查方法
第3章執行摘要
第4章 市場洞察
- 市場概況
- 產業吸引力-波特五力分析
- 供應商的議價能力
- 買家的議價能力
- 新進入者的威脅
- 替代品的威脅
- 競爭對手之間的競爭
- 產業價值鏈分析
- COVID-19 市場影響
第5章 市場動態
- 市場促進因素
- 零時差攻擊和有針對性的 APT 的興起
- 需要有效的解決方案來儘早發現攻擊者
- 市場限制
- 遺留誘餌系統的使用率很高
第6章 市場細分
- 按部署
- 雲
- 本地
- 按組織規模
- 中小企業
- 大型企業
- 按服務
- 託管服務
- 專業服務
- 作者:Deception Stack
- 資料安全
- 應用程式安全
- 端點安全
- 網路安全
- 按最終用戶
- 政府
- 醫療
- BFSI
- 防禦
- 資訊科技/通訊
- 其他最終用戶
- 按地區
- 北美洲
- 歐洲
- 亞太地區
- 拉丁美洲
- 中東和非洲
第7章 競爭格局
- 公司簡介
- Illusive Networks
- Commvault Systems Inc.
- Smokescreen Technologies Pvt. Ltd
- Attivo Networks Inc.(Sentinelone Inc.)
- Rapid7 LLC
- Ridgeback Network Defense Inc.
- Akamai Technologies Inc.
- Acalvio Technologies Inc.
- CounterCraft SL
- CyberTrap Software GmbH
- Fidelis Cybersecurity Inc.(Skyview Capital LLC)
- LogRhythm Inc.
- WatchGuard Technologies Inc.
- NTT Security Limited(Nippon Telegraph and Telephone Corporation)
- Broadcom Inc.(Symantec Corporation)
第8章投資分析
第9章:市場的未來
The Deception Technology Market size is estimated at USD 2.60 billion in 2025, and is expected to reach USD 5.18 billion by 2030, at a CAGR of 14.75% during the forecast period (2025-2030).
Key Highlights
- Deception technology is an advanced security solution to detect and prevent targeted attacks. Deceptions are achieved through purposeful obstructions, incorrect responses, misdirection, and forgery.
- Owing to the higher level of cyber threats, there is an increasing need for organizations to detect and mitigate advanced risks that have already breached the network. It is boosting deception technology adoption.
- The current security tools have effectively flagged anomalies but need to be more significant in defining their impact and risk potential. These tools generate many alerts, most of which must be investigated by security teams despite many of them being a waste of time. The resources are spent wastefully assessing these false threats, while the real and present threats must be addressed. By altering the asymmetry of an attack, deception technology helps security teams focus on real threats to the network. Scenes like these have aided the deception technology to gain momentum over the forecast period.
- Many deception solutions have AI and machine learning (ML) built into their core. These features ensure that deception techniques are kept dynamic and help reduce the operational overheads and the impact on security teams by freeing them from continually creating new deception campaigns.
- There was a sharp rise in cyberattacks harming individuals, businesses, and organizations during the COVID-19 outbreak. Consequently, several impacted enterprises are investing in upgrading outdated systems, thereby contributing to the deception technology market. For instance, the US Department of Homeland Security warned about emerging pandemic-related cybercriminals and advanced persistent threat groups. Interpol released a warning about criminals deliberately targeting medical facilities.
Deception Technology Market Trends
Network Security is expected to grow at a higher pace
- A zero-day attack is a targeted attack in which the attacker discovers software vulnerabilities and exploits them with other hackers until the organization becomes aware of the vulnerability. The zero-day exploit leaves no opportunity for detection initially.
- In 2021, Mandiant Threat Intelligence found 80 zero-day exploits in the wild, which was more than twice as many as the year before. The main actors exploiting zero-day vulnerabilities continue to be state-sponsored organizations with Chinese groups as leaders. The proportion of financially motivated actors deploying zero-day exploits has also increased significantly, with nearly one in every three identified actors exploiting zero-day exploits in the year before being financially motivated.
- Further, threat actors most commonly exploited zero-day vulnerabilities in Microsoft, Apple, and Google products, which reflects the popularity of these manufacturers. The significant growth in zero-day exploitation in the previous year, as well as the diversification of actors exploiting them, broadens the risk portfolio for businesses in practically every industry area and geography, particularly those that rely on these widely used systems.
- According to the research, a variety of factors contribute to an increase in the number of zero-day exploits. For example, the continued adoption of cloud hosting, mobile, and Internet-of-Things (IoT) technologies increases the volume and complexity of Internet-connected systems and devices. In other words, more software leads to more software flaws. The rise of the exploit broker industry is also likely contributing to this trend, with more resources being moved into zero-day research and development by private organizations, researchers, and threat groups alike.
- Due to the increase in zero-day attacks and APTs, organizations worldwide are deploying deception technologies to detect attacks as early as possible and minimize their effect on sensitive data. Therefore, the growing costs of data breaches, as indicated in the graph, are expected to drive the deception technology market during the forecast period.
North America is Expected to Hold Major Market Share
- The North American region is expected to hold a significant share in the global deception technology market owing to the increasing adoption of deception technology solutions in highly regulated industries such as financial services, health care, and government. Several US states, most notably California with its California Consumer Privacy Act (CCPA), have enacted privacy laws, significantly driving the demand for deception technology solutions among end-user industries.
- California passed a law, separate from the California Consumer Privacy Act, addressing default passwords on IoT devices and IoT vulnerabilities. Owing to this, the National Cybersecurity and Communications Integration Center (NCCIC) introduced the Technical Alert (TA), which provides information and guidance to assist MSP customer network and system administrators with the detection of malicious activity on their networks and systems and the mitigation of associated risks.
- This TA provides an overview of the TTP that APT actors use in MSP network environments, suggestions for mitigation, and details on reporting incidents. The high availability of adequate infrastructure, the presence of numerous global financial institutions, the high frequency of cyber-attacks, and the increased adoption of technologies are expected to drive the growth of the deception technology market in the North American region.
- The major trends responsible for the growth of deception technology in the North American region include the growing number of smartphone devices and an increase in the adoption of social apps, which generate sample data that contains valuable information. This has significantly increased the risk of cyber threats.
- In addition, the presence of prominent market vendors and increasing data volume in various organizations are driving the demand for deception technology solutions in the region. Furthermore, the early adoption of advanced technologies, such as 5G, AI, cloud, and IoT, in various end-user sectors is driving the demand for deception technology solutions at a rapid pace.
Deception Technology Industry Overview
The deception technology market is highly fragmented, with the presence of major players like Illusive Networks, Commvault Systems Inc., Smokescreen Technologies Pvt. Ltd., Attivo Networks Inc. (Sentinelone Inc.), and Rapid7 LLC. Players in the market are adopting strategies such as partnerships, innovations, mergers, and acquisitions to enhance their product offerings and gain a sustainable competitive advantage.
In February 2023, Rapid7 and the University of South Florida (USF) announced a partnership to create a cyber threat intelligence laboratory that will support interdisciplinary research efforts by faculty experts and students from four colleges and myriad disciplines.
In September 2022, Commvault announced the general availability of Metallic ThreatWise, an early warning system that proactively surfaces unknown and zero-day threats to minimize compromised data and business impact.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions and Market Definition
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET INSIGHTS
- 4.1 Market Overview
- 4.2 Industry Attractiveness - Porter's Five Forces Analysis
- 4.2.1 Bargaining Power of Suppliers
- 4.2.2 Bargaining Power of Buyers
- 4.2.3 Threat of New Entrants
- 4.2.4 Threat of Substitutes
- 4.2.5 Intensity of Competitive Rivalry
- 4.3 Industry Value Chain Analysis
- 4.4 Impact of COVID-19 on the Market
5 MARKET DYNAMICS
- 5.1 Market Drivers
- 5.1.1 Growing Number of Zero-day and Targeted APT's
- 5.1.2 Need of Effective Solutions for Early Detection of Attackers
- 5.2 Market Restraints
- 5.2.1 High Usage of Legacy Honeypots
6 MARKET SEGMENTATION
- 6.1 By Deployment
- 6.1.1 Cloud
- 6.1.2 On-premise
- 6.2 By Organization Size
- 6.2.1 Small and Medium Enterprises
- 6.2.2 Large Enterprises
- 6.3 By Service
- 6.3.1 Managed Services
- 6.3.2 Professional Services
- 6.4 By Deception Stack
- 6.4.1 Data Security
- 6.4.2 Application Security
- 6.4.3 Endpoint Security
- 6.4.4 Network Security
- 6.5 By End-User
- 6.5.1 Government
- 6.5.2 Medical
- 6.5.3 BFSI
- 6.5.4 Defense
- 6.5.5 IT and Telecommunication
- 6.5.6 Other End-Users
- 6.6 By Geography
- 6.6.1 North America
- 6.6.2 Europe
- 6.6.3 Asia Pacific
- 6.6.4 Latin America
- 6.6.5 Middle East and Africa
7 COMPETITIVE LANDSCAPE
- 7.1 Company Profiles
- 7.1.1 Illusive Networks
- 7.1.2 Commvault Systems Inc.
- 7.1.3 Smokescreen Technologies Pvt. Ltd
- 7.1.4 Attivo Networks Inc. (Sentinelone Inc.)
- 7.1.5 Rapid7 LLC
- 7.1.6 Ridgeback Network Defense Inc.
- 7.1.7 Akamai Technologies Inc.
- 7.1.8 Acalvio Technologies Inc.
- 7.1.9 CounterCraft SL
- 7.1.10 CyberTrap Software GmbH
- 7.1.11 Fidelis Cybersecurity Inc. (Skyview Capital LLC)
- 7.1.12 LogRhythm Inc.
- 7.1.13 WatchGuard Technologies Inc.
- 7.1.14 NTT Security Limited (Nippon Telegraph and Telephone Corporation)
- 7.1.15 Broadcom Inc. (Symantec Corporation)











